Piracy guide for onlyfans
the tl;dr on the resources
FreeBSD & Linux disk encryption comparison:
- FreeBSD: Uses
geli/gbdetools with simple/etc/fstabconfiguration (add.elior.bdesuffix) to encrypt swap and block devices. - Linux: Uses dm-crypt (kernel-level encryption) with LUKS as the standard frontend via
cryptsetuptool. LUKS provides metadata headers, multiple passphrase slots, and broad compatibility (VeraCrypt, BitLocker, etc.). - cryptsetup features: Supports LUKS (standard), plain mode, hardware OPAL drives, and operations like
luksFormat,open,close, and key management. Critical: LUKS header damage = permanent data loss. - Rolling vs. fixed releases: Rolling distros (Arch, Gentoo) offer latest features but less stability; fixed releases (Ubuntu, RHEL) prioritize stability—better for production.
Bottom line: Both OSes offer robust block encryption—FreeBSD via simple fstab modifications, Linux via the mature dm-crypt/LUKS ecosystem.
Table of Contents
- Importing
- Cryptography/Canary (to verify PGP et al)
- Uploading scripts
- Operating Systems and Docker
- Imagemagick commands
- From the coomer board
- Moreno address
 see doxing.
see doxing.
Actual motive: A science, thanks Crystal et al.
Tell crystal to eat my butt
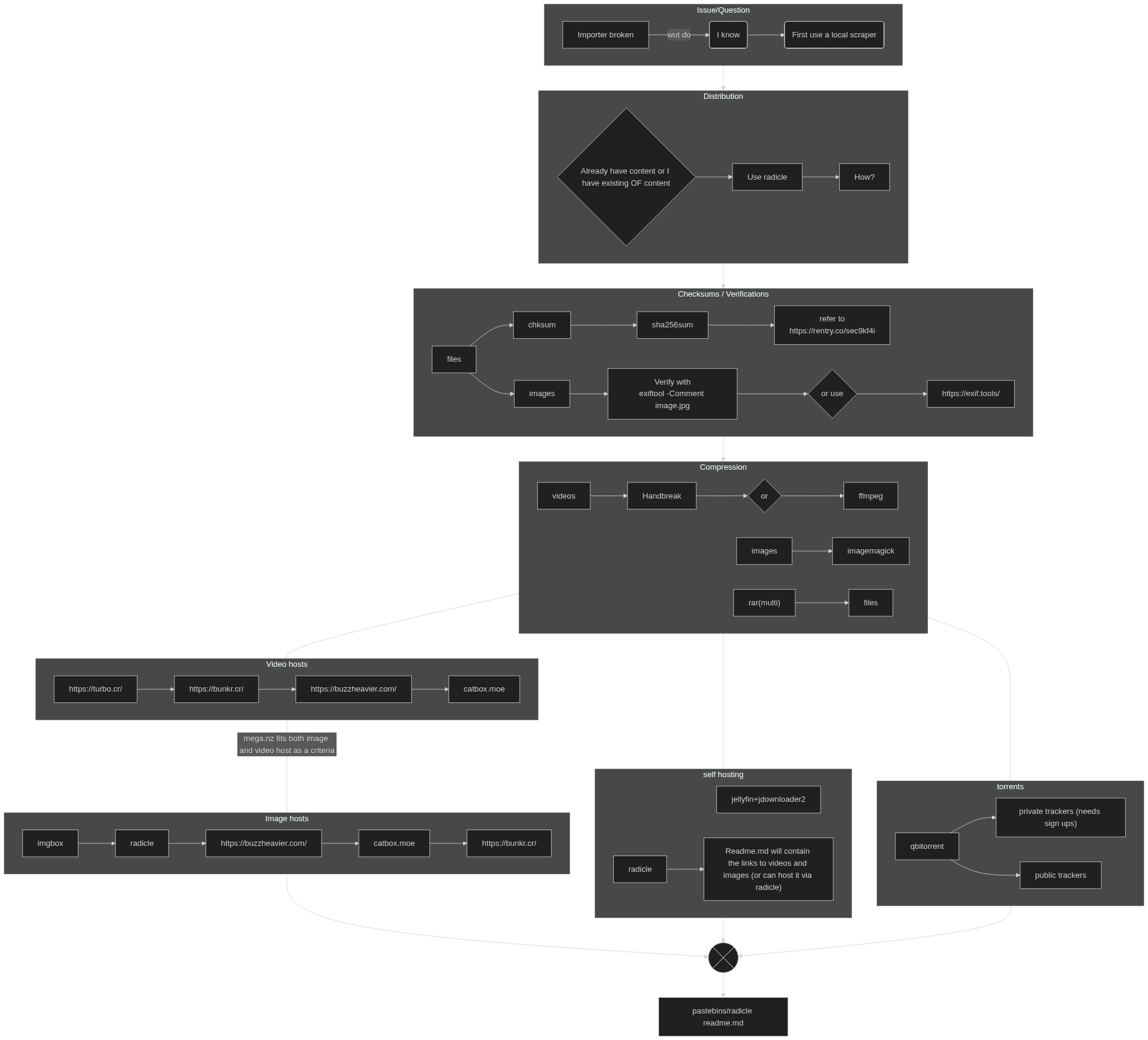
Importing
First get the correct keys
Can be found in cookies -> auth_id.
Can be found in local storage -> bcTokenSha. Paste localStorage.bcTokenSha into the console for easy access.
It's all the same as patron piracy but without the extra steps for Patron, just need a session key/1.
And a user-agent, use this default:
If you cannot figure this out, then I cannot help you any further lmao.
Cryptography/Canary (to verify PGP et al)
Use a PGP signing tool such as Kleopatra for this.
Import these
This is great if you're going to do a file upload via radicle or another file host for images and videos.
Specifically those that have harder take down notices such as buzzheavier OR if you are going to torrent or do a multi-rar.
If you are going to upload videos to turbo.cr and images to a filehosting site that strips the hashes/metadata (such as imgbox) then skip this step and head right down to operating systems and docker.
cksum, sha256sum, MD5
cksum computes a basic CRC checksum (32-bit), byte count, and filename for files—great for quick integrity checks on transfers. Output looks like: 123456789 1024 filename.txt (checksum, bytes, name).
sha256sum generates a secure 256-bit SHA-256 hash, ideal for verifying downloads against tampering or corruption. Output: e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 filename.txt (hash, filename).
Basic Usage
Run on a single file:
| command | integrity | security checks | Great to check for |
|---|---|---|---|
| cksum | Yes | No | Only for corruption of files |
| sha256sum | Yes | Yes | Tampering of files and corruption of files |
| MD5sum | Yes | No | Quick Integrity check. |
Both work on stdin too: echo "test" | cksum or echo "test" | sha256sum.
Verify Checksums
Generate first: sha256sum bigfile.iso > checksum.txt (saves hash to file).
Check: sha256sum -c checksum.txt—says "OK" if matches, warns on mismatch (exit code 1 for scripting).
cksum supports --check similarly but is less collision-resistant; prefer sha256sum for security.
Quick Tip
- Multiple files:
sha256sum *.txtlists all. - Compare manually: Copy the hash, run command, eyeball it.
file hashing guide:
Quick script to verify (shebang):
It should save the hashes next to the files as the filename as a text file
- Will show partial hashes
- Should work with files such as video files and image files
- IT GLOWS
Verification example:
if not verified, it will be red and will not match the hash. Always provide hashes.
✗ Posts/Images/2316x3088_26c69c0bdb9da377209b12707ff9816b.jpeg - No matching hash found.
SHA (partial): c83a2408
CKSUM (partial): 85526641
Instead of green [32m✓ Posts/Images/2316x3088_26c69c0bdb9da377209b12707ff9816b.jpeg [0m → Posts
Images/2316x3088_26c69c0bdb9da377209b12707ff9816b.jpeg (SHA: 4cedfa3b, Size: 2299574 bytes)
These can be inside radicle as links.txt with catbox as a multirar. (see Rename to right files from terminal)
Image files
to add into image files:
WARNING RETARD!!!! THIS WILL DO THIS IN EVERY FILE IN A DIR IF DONE WRONG!!!
can do this with videos, just append *.mp4 and rename the text file to video_hashes.txt
Export your hashes from the images when veryfying
sha256sum *.jpeg > image_hashes.txt
sha256sum --check image_hashes.txt
add this into the readme.md or into a textfile inside radicle (if using a filehost).
uploading scripts
Catbox uploader modified
Rename to right files from terminal (catbox)
Operating systems and Docker
OS of choice
Can be any distro, server can work well enough as everything stored in tmpfs is not written inside/to the disk itself.
if you're gonna use a server, use Debian or Ubuntu but don't use a rolling distro.
create a tmpfs partition scheme, replace /home/user/folder with something else to where the user (YOU) can write in
This will generate a new radicle identifier each time a docker image is built, everything on temp will be nuked upon reboot as it's stored in the system ram.
do NOT and I mean DO NOT store the docker container in /tmp as that's system wide.
Docker (radicle)
radicle commit:
I wouldn't change the following fields:
- the dir, that is the name of the repo initialized with git and radicle. This would reduce noise (Think DID key/account re-generation).
- description
- name/email
- commit message
- Don't place yml file outside tmpfs and build it, otherwise you'd have written data to a potentially unsecure device (unless if it's encrypted).
- Radicle also tracks commit messages and history so be mindful of what you do with git and don't be an idiot.
#!/bin/sh
# Be sure you're not in the target dir, just in the home dir please.
mkdir ~/init && cd ~/init && cp -R ~/targetdir/* ./
# Initialize git repository (in current directory /var/lib/radicle/init)
git init
# Set git global config
git branch -m main
git config --global user.email "[email protected]"
git config --global user.name "Your Name"
# Increase buffer size
git config --global http.postBuffer 524288000
# this commit message can be anything really.
# add the shit you need with git add
git add readme.md Images cksum.sh
git commit -m "."
# THEN: Run rad init
rad init
sleep 20
rad self
sleep 20
rad node status
|
to build/run everything do this:
shut it down goyim.
fix the container on the host drive for the directory it's mounted on docker.
Suppose container runs as UID 1000, GID 1000
First verify, if it's ID 1000, GID 1000 it isn't owned by the container.
Then do this
Imagemagick commands
The following commands for imagemagick should work great depending on your use case!
replace 256x256 output.jpg with 256x256+2+2 -tile 4x4 output.jpg if you must. This is great for imgbox and possibly radicle as these are Optimal.
you don't need to include padding in the montage images.
-tile controls how much tiles are inside the montage
-geometry controls the size of the output images
+2+2 is just padding of the source images which will be resized see above.
YOU are ENCOURAGED to experiment and contribute I am only one freeman.
Optimal setting for imagehosts and radicle
Not Optimal for any image host, but good for torrents possibly or a file upload such as buzzheavier.
Backgrounds
Limits on memory
force everything to disk
force everything to the /tmp folder
7G ram
it depends on system resources, results may vary but I'd try as seen below.
To diagnose enter this command, useful for running on 7GB Force Disk-Based Processing. Be sure to hit ctrl+c after a few minutes
Mem stats:
While on a Desktop Environment
Take this information and commands as you will, this will and should be able to help you as I do not want to make this long as it is.
Trouble shooting:
to show
docker network ls
docker volume ls
docker container ls
Remove
docker container ls
docker volume ls
docker network ls
see what's running
docker ps -all
for all the commands issue the command in the respected command such as rad or docker.
from the coomer board:
Curated list(s) of everything known to man:
FMHY (yes use all caps) for zerobin password.
| Title / Category | Link | Description |
|---|---|---|
| FMHY Porn list | https://www.zerobin.net/?1d980b20c690ead0#Zr3uv+UJz57qUHyz+u1GvXgGwFIo/PPry6VoW9Qlsq0= | Curated porn list from FMHY. |
| FMHY main index | fmhy.net | Central hub for the “Free Media Heck Yeah” project—organized collections of free and open-source tools, sites, and guides. |
| FMHY: Video Tools | fmhy.net/video-tools | Section of FMHY focusing on video-related utilities (editing, converting, downloading, compressing, etc.). |
| FMHY: Processing & Encoding | fmhy.net/video-tools#processing-encoding | Subsection covering video post-processing and encoding tools. |
Scrapers from github/radicle search for simple piracy search
OF-DL has a friendly GUI while OF-Scraper is CLI only.
the auth file should be placed in where you built everything such as ../../OF-DL/OF DL.Gui/bin/Release/net10.0/
refer to the docs
| Name | URL |
|---|---|
| Radicle Search | https://search.radicle.xyz/ |
| OF-Scraper | https://github.com/datawhores/OF-Scraper |
| OF-DL | https://git.ofdl.tools/sim0n00ps/OF-DL |
| Discord Exporter | https://github.com/tyrrrz/discordchatexporter |
| OnlyFans Cookie Helper Releases | https://github.com/M-rcus/OnlyFans-Cookie-Helper/releases |
| OF-DL-Auth-Helper | https://github.com/whimsical-c4lic0/OF-DL-Auth-Helper/releases |
| Patreon Downloader | https://github.com/patrickkfkan/patreon-dl |
| Fansly GitHub Search | https://github.com/search?q=fansly&type=repositories |
Wikis
Archival
| Name/Description | URL/Link | Notes |
|---|---|---|
| ArchiveBox | https://archivebox.io/ | Self-hosted internet archiving tool |
| Archive.today | https://archive.today | Web snapshot service that saves pages on demand |
| Internet Archive (Wayback Machine) | https://web.archive.org | Large-scale web archive preserving historical website versions |
| The Permanent Booru | https://git.sr.ht/~kycklingar/PBooru | uses decentralization of IPFS to distribute its content. Build from source. Check if current node is down. |
| FMHY Internet Archiving Tools | https://fmhy.xyz/internet-tools#archiving | Directory of free internet and archiving tools |
Video hosts / file
| Video Host / File | URL | Notes |
|---|---|---|
| Turbo | https://turbo.cr/ | file size is limited, easy account creation. |
| Buzzheavier | https://buzzheavier.com/ | file size isn't limited, but isn't permanent. |
| Catbox | https://catbox.moe | Isn't permanent as it says, file size is limited. |
| Bunkr | https://bunkr.cr | Use bunkr-albums if it’s down |
Archiving tools (zips/rars/etc for multirar)
| Category | Tool/Option | Platform | Notes / Link |
|---|---|---|---|
| Archiving Tools (ZIPs/RARs/Multivolume) | WinRAR | Windows (also available on Linux via Wine) | Popular for creating and extracting RAR, ZIP, and multi-volume archives |
| 7-Zip | Windows, Linux (via p7zip) | Open-source alternative supporting many archive formats | |
| Linux Archiving Utility | Ark | Linux (KDE environment) | https://apps.kde.org/ark/ — Native archive manager for KDE desktop |
DO NOT EVER and I mean EVER use telegram unless if you like 'p.
private messaging apps:
| Name / Description | Link | Notes |
|---|---|---|
| signal | https://signal.org/ | Secure but needs a mobile phone number. |
| simplex | https://simplex.chat/ | Is the most secure but isn't as audited. |
| telegram | https://desktop.telegram.org/ | Not E2E by default. |
| fluxerapp | https://fluxer.app/download | Can be installed on android/discord replacement |
Alts
| Name / Description | Link | Notes |
|---|---|---|
| Sexy e-Girls | https://sexy-egirls.com/ | Can upload content/piracy. |
| celebforum | https://celebforum.to/ | German/Forum. |
| simpcity | https://simpcity.cr/ | Need points to post on OF. |
| bbw-chan | https://bbw-chan.link/ | BBW/fetish specific. |
| Copies off coomer.su (onlyfans) | https://leakedzone.com/ | loads better but can fail sometimes. |
| you can see more at FMHY Porn list. | ||
| also the porndude. |
Filehosts
udrop can be up to 50 GB but can get taken down, thotpacks is membersonly same with empornium and sexy-egirls I'm not sure about re-uploading content but you may try; seems to be a piracy site itself.
| Name / Description | Link | Notes |
|---|---|---|
| UDrop | https://www.udrop.com/ | |
| Thotpacks | https://thotpacks.xyz/ | |
| Empornium | http://about.empornium.ph/ | |
| Reddit Thread – OnlyFans Piracy Discussion | https://www.reddit.com/r/Piracy/comments/rsxpyn/onlyfan_torrentpiracy/ | |
| Mega – 20 GB free storage (expandable with tools) | https://mega.io/ | |
| Cloud Storage Tools (FMHY) | https://fmhy.net/file-tools#cloud-storage | |
| Mega Account Creation Tools (FMHY) | https://fmhy.net/file-tools#mega-tools | These tools actually work, but you'll need to sign in with some of these tools; it up to others to download or for you to torrent or mirror. |
| Catbox Uploader (GitHub, see above for mod) | https://github.com/karimawi/CatboxUploader |
Self hosting:
| Name / Description | Link |
|---|---|
| Radicle – decentralized code collaboration | radicle/docker image |
| Salvatorenoschese PrivateBin (supports images) | https://bin.salvatorenoschese.it |
| Linux/Mac Self-Hosting Tools (FMHY) | https://fmhy.net/linux-macos#server-selfhosting |
| yt-dlp supported sites list | https://github.com/yt-dlp/yt-dlp/blob/master/supportedsites.md |
| Jellyfin + JDownloader2 local hosting guide | https://jhx7.de/blog/media-hosting-locally-with-jd-and-jellyfin/ |
| Jellyfin networking documentation | https://jellyfin.org/docs/general/post-install/networking/ |
| Tailscale + Mullvad documentation | https://tailscale.com/mullvad |
lossless videos (editing etc)
| Tool | Description | Key Use Case | Link/Source |
|---|---|---|---|
| LosslessCut | FFmpeg-based GUI for trimming, cutting, and editing videos/audio/subtitles without re-encoding—extremely fast for precise lossless operations. | Quick edits like cutting clips while preserving original quality. | LosslessCut |
| HandBrake | Open-source transcoder supporting lossless modes (e.g., H.264/H.265 at high quality settings like CRF 0-18) to shrink files while keeping all data intact. | Encoding for smaller storage/transmission without quality degradation. | git/site |
email gen
| Purpose | Tool / URL | Notes |
|---|---|---|
| Email generation (cock-li) | cockli-gen on GitLab | Generates cock.li-style emails. Some platforms may reject cock.li domains. |
| Alternative: Secure email setup | ProtonMail + KeePassXC | Use ProtonMail for email. KeePassXC can generate a random username and password. |
| Simple username + password generation | Username Generator (Firefox Add-on) | Quick tool for creating usernames and simple passwords. |
| No email required | KeePassXC | Use KeePassXC alone to generate and store usernames/passwords for accounts that don’t need an email. |
VPNs:
Here’s a clean table version:
| VPN | Port Forwarding Support | Notes |
|---|---|---|
| Proton VPN | Partial | Limited port forwarding support |
| Private Internet Access | Full | Supports port forwarding fully; owned by Kape |
| Mullvad | Not native (workaround) | Use Tailscale with Mullvad exit nodes for port forwarding capability |
Patron Piracy
For Patron specifics this basically works just like most onlyfans rippers out there see importing
For the specific tools I use it's patreon-dl, as that can be used in any folder inside your OS.
But hold on cowboy, you'll need to install FFmpeg then install deno as described inside it's readme.md which describes it's limitations. Also comes with a GUI
And there's also PatreonDownloader which can be build by dotnet if that's your thing. Read the main readme as that is important on how to run this.
Links:
| # | Resource Link | Description / Notes |
|---|---|---|
| 1 | coomer thread/1 | A thread that is copy pasted and hosted here |
| 2 | cypherpunk manifesto | cypherpunk manifesto, privacy =/= secrecy. Hoes need to read this. |
| 3 | The Piracy Glossary | Piracy glossary, for those who dare sail the seven seas |
| 4 | Porn Quitting | Porn quitting, for those who need it. |
| 5 | Guerilla Open Access Manifesto | Information is power. But like all power, there are those who want to keep it for themselves. Hoes also need to read this. |
Resource:
| # | Resource Link | Description / Notes |
|---|---|---|
| 1 | Whipped_Love | An example of Whipped_Love hosted on the Radicle project resource (peer-to-peer). |
| 2 | FreeBSD Handbook – Swap Encryption | Documentation for encrypting swap space in FreeBSD 13.0. |
| 3 | RHEL 5 Installation Guide – Disk Encryption | Red Hat documentation on encrypted installations and LUKS. |
| 4 | DMCrypt Wiki (Cryptsetup) | Overview and internal details of dm-crypt on GitLab. |
| 5 | Cryptsetup GitLab Repository | Main repository for the cryptsetup tool. |
| 6 | cryptsetup(8) Man Page – Arch Linux | Manual entry for the cryptsetup command on Arch Linux. |
| 7 | Arch Wiki – dm-crypt | Arch Linux documentation covering dm-crypt and encryption setups. |
| 8 | ZDNet Archive – Rolling vs Fixed Release | Archived article discussing Linux release models. |
| 9 | WiseGeek Archive – What Is a Rolling Release? | Archived explainer on rolling release Linux distributions. |
| 10 | GeeksforGeeks – Rolling vs Fixed Linux Distros | Comparison between rolling and fixed Linux distros. |
| 11 | Rentry Page | Hashes. |
| 12 | Archive.ph Snapshot (of Rentry) | This rentry. |
| 13 | OSINT Toolist |
Moreno address:
lost edit key to previous rentry
- Zodiac